You are here
Tracebox
Description:
Tracebox is an open source topology discovery software that has been developped by the Université de Liège et by the Université catholique de Louvain in Belgium. Tracebox is an extension to the widely used traceroute tool. The objective of tracebox is to detect various types of middlebox interference over almost any path. To do so, tracebox sends IP packets containing TCP segments with different TTL values and anlyses the packet encapsulated in the returned ICMP message. Further, as recent routers quote, in the ICMP message, the entire IP packet that they received, tracebox is able to detect any modification performed by upstream middleboxes. In addition, tracebox can often pinpoint the network hop where the middlebox interference occurs.
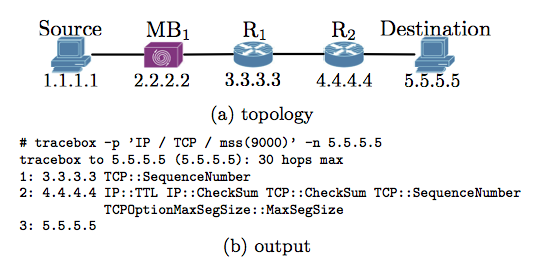
The figure above ((a) topology) shows a simple network, where MB1 is a middlebox that changes the TCP sequence number and the MSS size in the TCP MSS option but that does not decrement the TTL. R1 is an old router while R2 is a router that is able to quote, in the returned ICMP message, the entire message that is responsible of the problem. The server always answer with a TCP reset. The output of running tracebox between ``Source'' and ``Destination'' is given by the below part of the figure ((b) output). The output shows that tracebox is able to effectively detect the middlebox interference but it may occur at a downstream hop. Indeed, as R1 does not quote the full packet, tracebox can only detect the TCP sequence change when analyzing the reply of R1. Nevertheless, when receiving the full message quoted from R2, that contains the complete IP and TCP header, tracebox is able to detect that a TCP option has been changed upstream of R2. At the second hop, \tracebox shows additional modifications on top of the expected ones. The TTL and IP checksum are modified by each router and the TCP checksum modification results from the modification of the header.
Tracebox comes in three flavours:
- The original software, written in C++, allows some LUA embedding to easily extend tracebox capabilities. This is particularly interesting for discovering new types of middleboxes. This version supports two types of output: text (on the standard output) and pcap files.
- tracebox has been ported into scamper, an integrated tool for topology discovery. scamper comes with interesting tools in the context of mPlane: ping, traceroute (various implementations), Doubletree, TBit, ... scamper allows for IPv4 and IPv6 network probing. tracebox into scamper supports two types of output: text (on the standard output) and warts files (warts is a binary format for storing packets into the scamper system).
- tracebox has been ported into the Android system in order to support some mPlane use cases. Due to limitations inherent to mobile systems, the Android tracebox is a kind of light version of the original one. The output is sent to a back office where any kind of manipulation is made possible.
Tracebox important features:
tracebox brings two important features.
- Middleboxes Detection. tracebox allows one to easily and precisely contral al probe packets sent (IP header, TCP or UDP header, TCP options, payload, etc). Further, tracebox keeps track of each transmitted packet. This permits to compare the quoted packet sent back, in an ICMP time-exceeded message by an intermediate router, with the original one. By correlating the different modifications, tracebox is able to infer the presence of middleboxes.
- Middleboxes Location. using an iterative technique (in the fashion of traceroute) to discover middleboxes also allows tracebox to approximately locate, on the path, where modificationsoccured and so the approximate position of middleboxes.
Quick start:
Original Software
The original software is freely available at tracebox.org (with the source code). The software works under Mac OS X, BSD, and Linux distribution. If you are under Mac OS X, the easiest way to install tracebox is to run homebrew (brew install tracebox).
Source can be found at http://www.github.com/tracebox/tracebox.
Tracebox requires:
- The development package of libpcap, (lib)lua >= 5.1.
- Automake, autoconf and libtool.
To build Tracebox:
$ ./bootstrap.sh
$ make
$ sudo make install
There are two possible ways to use tracebox either with the Python scripts (see some samples scripts in /tracebox/examples) or with the default binary. The later only sends one TCP probe and look for changes in the path.
Scamper Port
The current snapshot of scamper's source code is cvs-20140404 and do not contain Tracebox. Scamper should compile and run under FreeBSD, OpenBSD, NetBSD, Linux, MacOS X, Solaris, Windows, and DragonFly. All releases of scamper are licensed under the GPL v2.
Scamper with tracebox can be found at: https://github.com/fp7mplane/components/tree/master/scamper/source
To build Scamper:
$ ./configure
$ make
$ sudo make install
The Scamper Tracebox implementation is the most complete and efficient. It involves different options to modify the text output format (e.g: traceroute-like output vs simplified middlebox locations only output, add the ICMP quoting size standard used by each hop, ... ). It also contains other non-tracebox middlebox detection methods that are not interface within mPlane.
Android Port
The tracebox Android port is available at androidtracebox.org (with the source code).
To install tracebox Android:
- Root your mobile phone (it is impossible to forge packet without the right privileges)
- Install tracebox Android from the Play Store.
tracebox Android usage is very intuitive. You can either enter yourself a destination to probe or download, from the back office (the source code of the back office is also available), a targets file.
mPlane proxy interface
The current mPlane Tracebox interface is part of the scamper component and contains 3 capabilities (each one subdivided for IPv4/IPv6):
- traceboxV_standard_capability: a simple tracebox probe over TCP without any options. V is the IP version.
- traceboxV_specific_capability: a tracebox probe that you can precisely specify by choosing IP fields value (ECN, DSCP, IPID/IPFLOW), the transport layer (TCP or UDP) and various TCP options/features (MSS, WScale, ECN, MPTCP, ...).
- traceboxV_specific_quotesize_capability: the same probe description than traceboxV_specific_capability with an additional result column containing the ICMP quoting size standard used by each hop
New features supported by the mPlane project
Thanks to the support of the mPlane project we extended tracebox functionalities with the following features:
- tracebox port into scamper
- tracebox deployment on IPv6 infrastructure
- tracebox port into Android
Changes since D2.2
The tracebox has been merged into the Scamper component.